Monarch Gaming House Sign In Sophisticated Zero Trust Architecture United Kingdom
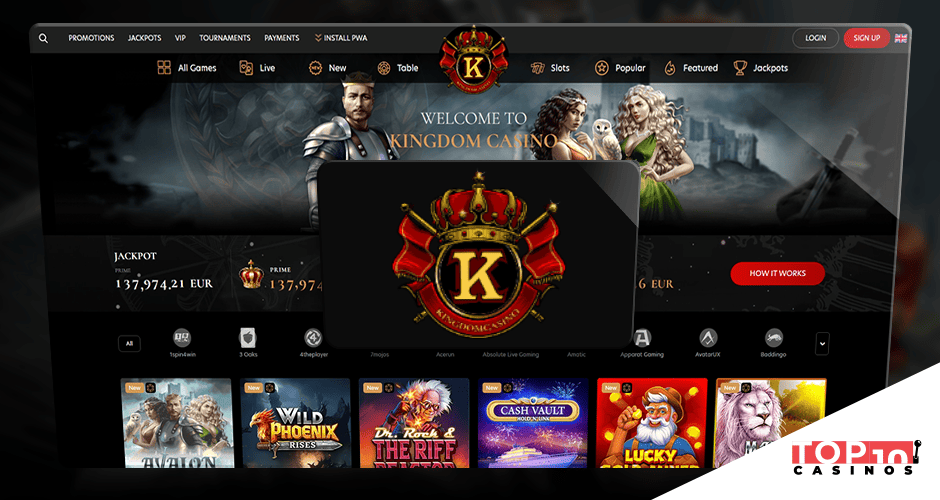

As we delve into Kingmaker Casino’s adoption of advanced Zero Trust Architecture (ZTA), casino sign in, it’s essential to acknowledge how this framework redefines security in online gaming. By emphasizing strict identity checks and continuous surveillance, we can examine the implications for user authentication and data protection. This preventive approach not only addresses potential threats but also shapes player trust in the system. What are the wider implications of such security measures for the prospect of online casinos?
Key Insights
- Implementing Zero Trust Architecture (ZTA) boosts security during Kingmaker Casino sign-ins by requiring authentication for every access attempt.
- Minimal access rights guarantees that players can only reach resources relevant to their roles, minimizing security risks.
- Multi-factor authentication (MFA) strengthens sign-in safety by integrating passwords with extra verification methods, lowering unauthorized access possibilities.
- Continuous monitoring of user behavior at Kingmaker Casino detects anomalies, enhancing scam identification and adaptive security measures.
- Adherence with data jurisdiction regulations in the UK matches Kingmaker Casino’s security strategies with regional rules, strengthening player trust.
Understanding Zero Trust Architecture
As we delve into Zero Trust Architecture (ZTA), it’s essential to understand that this model essentially alters how organizations handle security. Instead of presuming trust based entirely on network location, ZTA mandates thorough verification of identity and device integrity for every access attempt. We accept that implementing a zero trust framework requires us to adopt micro-segmentation and continuous monitoring, ensuring that data sovereignty remains intact. By properly recognizing users and devices, we can significantly mitigate risks linked to developing cyber threats. Additionally, ZTA’s focus on securing sensitive data—particularly as we navigate regulatory mandates—guarantees that compliance with data sovereignty laws becomes an integral part of our security strategy. In this complicated landscape, we must modify our security posture to foster resilience.
Importance of Cybersecurity in Online Gaming
In the domain of online gaming, cybersecurity plays a crucial role in securing both player data and the integrity of the gaming environment. As we participate in diverse platforms, we must understand the growing landscape of cybersecurity threats. These threats can range from data breaches to account takeovers, threatening not only individual player security but also the reputation of gaming operators. Implementing solid cybersecurity measures is essential for protecting sensitive information and preserving user trust. By using cutting-edge encryption techniques and continuous monitoring, we can effectively lessen risks linked to these threats. Additionally, fostering an informed gaming community aids us collectively counter cyber risks, guaranteeing a safe and enjoyable experience for everyone engaged in online gaming.
Key Principles of Zero Trust Implementation
Five key guidelines form the basis of the efficient deployment of a Zero Trust Architecture (ZTA) within internet gaming platforms. First, we must adopt a “verify before trust” mindset, making sure that all users and gadgets are authenticated and permitted before allowing access. Second, we should implement least-privilege access, restricting user permissions based on particular roles. Third, constant monitoring is crucial; we need to examine user conduct in live to spot anomalies. Fourth, we must incorporate strong encryption methods to secure private data, aligning with best security practices. Finally, continuous risk analyses will guide our implementation plans, permitting us to modify to new threats effectively. By adhering to these principles, we can enhance our data protection position in online gaming.
The Role of User Authentication in ZTA
User authentication serves an crucial function in the success of Zero Trust Architecture (ZTA), serving as the guardian for access to sensitive assets. By implementing multi-factor authentication (MFA), we introduce layers of security that greatly reduce the risk of unauthorized access. MFA necessitates participants to provide multiple forms of authentication, such as passwords enhanced by security tokens. These tokens, which can be tangible gadgets or software-based, boost our certainty in confirming user identification. Deploying a solid user authentication procedure ensures we can adaptively judge risk and adapt access based on environmental conditions. As we advance towards an comprehensive ZTA plan, refining our user authentication systems will be vital in ensuring the wholeness and confidentiality of information across our systems.
Enhancing Data Protection at Kingmaker Casino
Implementing advanced user authentication mechanisms sets the groundwork for enhancing data protection at Kingmaker Casino. By integrating strong security policies, we guarantee the confidentiality and integrity of sensitive player data. We prioritize data encryption, applying strict algorithms to safeguard information both in transit and at rest. This approach minimizes risks associated with unauthorized access, bolstering our overall security framework.
![]()
Furthermore, we regularly update our security policies to adapt to new threats, guaranteeing continuous improvement in our data protection strategies. Implementing multi-factor authentication works in tandem with encryption, providing multi-layered security that mitigates vulnerabilities. As we navigate the complexities of the gaming industry, our commitment to state-of-the-art data protection remains steadfast, fostering a secure environment for our players while adhering to best practices in cybersecurity.
Impact on User Experience and Player Confidence
While prioritizing advanced security measures at Kingmaker Casino, we also recognize the vital relationship between these enhancements and user experience, as well as player confidence. Our implementation of Zero Trust Architecture serves not just to safeguard sensitive data, but to bolster a seamless gaming experience. We’ve integrated user feedback mechanisms to guarantee we’re responsive to player needs, allowing us to refine our platforms continuously. This forward-thinking approach aligns with our player retention strategies, enhancing trust and satisfaction. By demonstrating our commitment to secure yet enjoyable gameplay, we foster a assured community that feels valued. Ultimately, merging robust security with top-notch user experience forms the backbone of our ongoing efforts to retain loyal players in a competitive market.
Future of ZTA in the Online Casino Industry
As we examine the future of Zero Trust Architecture in the online casino industry, we must consider how enhanced security measures will reshape player engagement. User identity verification protocols are set to evolve, providing a strong shield against fraud. By implementing sophisticated fraud prevention strategies, we can secure a safer gambling environment that builds trust and confidence among players.
Enhanced Security Measures
One essential element of the future of Zero Trust Architecture (ZTA) in the online casino industry lies in enhanced security measures crafted to combat progressively sophisticated cyber threats. By adopting solid security protocols, we can guarantee our systems are protected against unauthorized access. It’s vital that these protocols evolve to address not only the technical aspects but also adhere to privacy regulations that safeguard user data. We must utilize cutting-edge encryption methods and continuous monitoring practices that allow real-time identification of anomalies. This proactive approach enables us to maintain a secure environment while fostering trust among our users. As we welcome these innovations, we dedicate ourselves to establishing a strong framework that emphasizes privacy and security in an ever-evolving digital landscape.
User Identity Verification
The integration of user identity verification processes plays a significant role in the evolution of Zero Trust Architecture (ZTA) within the online casino industry. As we handle increased regulatory scrutiny and cyber threats, effective verification methods become imperative. Employing biometric verification, such as thumbprint or facial recognition, enhances our confidence regarding user identities. This technology offers a sophisticated layer of security that traditional methods can’t match. Coupled with two-factor authentication (2FA), which requires something the user knows and something the user has, we create a robust framework for identity assurance. By implementing these state-of-the-art verification approaches, we’re not only protecting user accounts but also bolstering the integrity of the entire gaming experience. Together, we can navigate the complexities of ZTA with confidence.
Fraud Prevention Strategies
While furthering Zero Trust Architecture (ZTA) principles, we must implement robust fraud prevention strategies to counter the dynamic landscape of online casino fraud. One of the most powerful tools at our disposal is machine learning. By leveraging advanced algorithms, we can evaluate vast amounts of data in real-time, identifying patterns indicative of fraudulent activity. Additionally, behavioral analysis allows us to comprehend user actions, identifying anomalies that traditional methods might miss. Together, these technologies create a robust framework that not only detects but also anticipates fraudulent behavior, continually adapting to new tactics employed by fraudsters. Through proactive engagement and constant refinement of our fraud prevention measures, we can ensure a safe gaming environment, cultivating player trust and loyalty in the process.
Conclusion
To recap, our commitment to advanced Zero Trust Architecture at Kingmaker Casino not only boosts the security of our users but also enhances their overall journey. By adopting rigorous verification processes and continuously monitoring user activity, we’re actively safeguarding confidential data against potential threats. As we progress, we remain committed to enhancing our security measures, ensuring that our users can experience a secure and trustworthy gaming atmosphere. The evolution of cybersecurity in internet gaming platforms has truly just started.

